Live Forms v7.4 is no longer supported. Please visit Live Forms Latest for our current Cloud Release. Earlier documentation is available too.
Manage Tenants
is a multi-tenant application. Tenants allow you to segregate groups of users and roles. Users from one tenant cannot access users in any other tenant. Note: this does not apply to public forms/flow which do not require login access to a tenant.
The In-house superuser admin can create as many tenants on your form server as needed. Once the superuser admin creates the tenant, the tenant admin user can then login to manage the tenant, configure LDAP, add users & roles, etc. See the Admin Home Page for differences between the superuser admin and tenant admin.
trial tenants in the cloud are initially configured with the frevvo Default security Manager. Once you have purchased your
license, you can switch the Security Manager of your tenant and retain existing forms/flows, users, roles and submissions.
Tenants using the Default Security Manager can be migrated to:
- Default Security Manager → LDAP
- Default Security Manager → SAML
- Default Security Manager → Azure SAML
Tenants using the LDAP Security Manager can migrate to:
- LDAP → SAML
- LDAP → Azure SAML
If you want to switch the security manager of your tenant, cloud customers should contact sales@frevvo.com to initiate the procedure.
On this page:
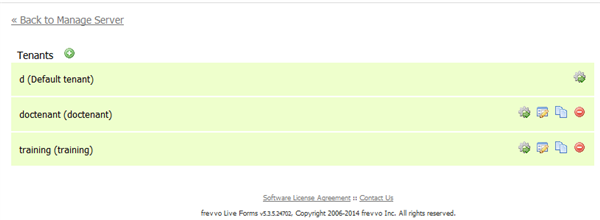
Manage Tenants
The superuser for in-house customers can add new tenants to your
server using the Manage Tenants page.
- Click to add a new tenant.
- Click to display the Manage Tenant page. You use the links on this page to edit the tenant information and manage the tenant's roles, users, form and control categories, and production forms.
- Click to edit the tenant information. This link displays the same page as the Edit Tenant link on the Manage Tenant page.
- Click to make a copy of the tenant.
- Click to remove the tenant from the server.
You cannot remove or copy the d (Default tenant).
Add Tenant
The superuser for in-house customers can use the Tenant page to add a new tenant . We recommend using lower case for the tenant name as the tenant name becomes part of your user's login names which are case sensitive.
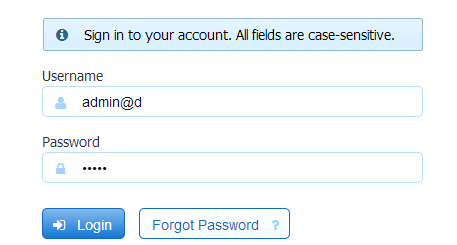
To display the Tenant page,
- Login as the superuser admin. Enter admin@d as the userID and admin as the password (if you did not change it). Click Manage Tenants.
- Click the plus icon to add a new tenant.
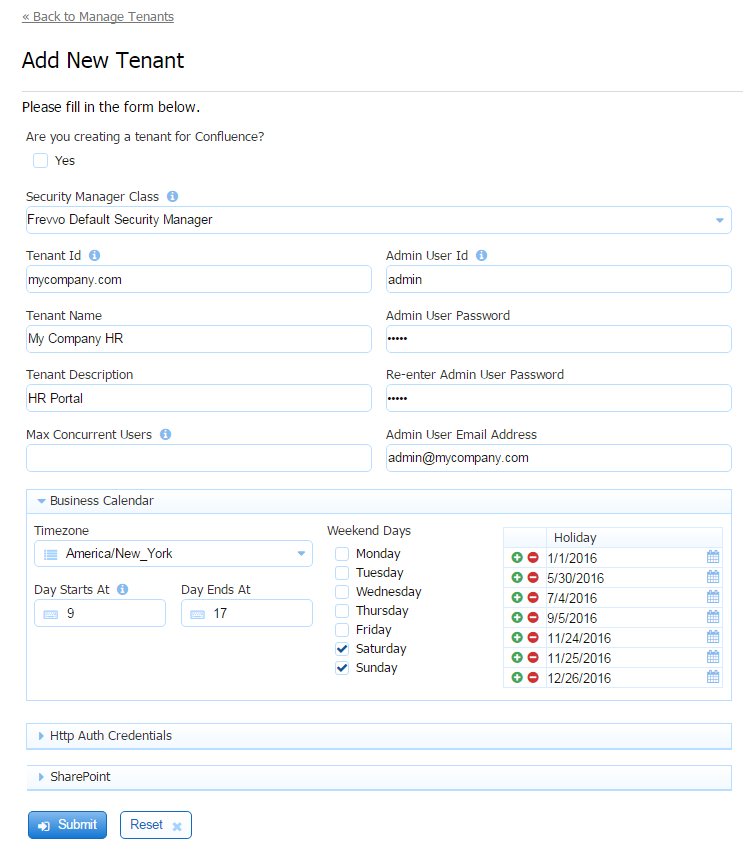
- Fill in the fields with the information for your new tenant.
- Click the Submit button to save.
Here is a brief explanation of the fields:
Are you creating a tenant for Confluence? - Check this if you are planning on integrating
with Confluence. If checked, the Security Manager Class field displays the Delegating Security Manager - This is the Security Manager needed for Confluence. The SharePoint section of the screen is hidden. The SharePoint Connector is not available to frevvo Confluence customers as it will not work in embedded scenarios. If unchecked, the Default Security Manager will be used.
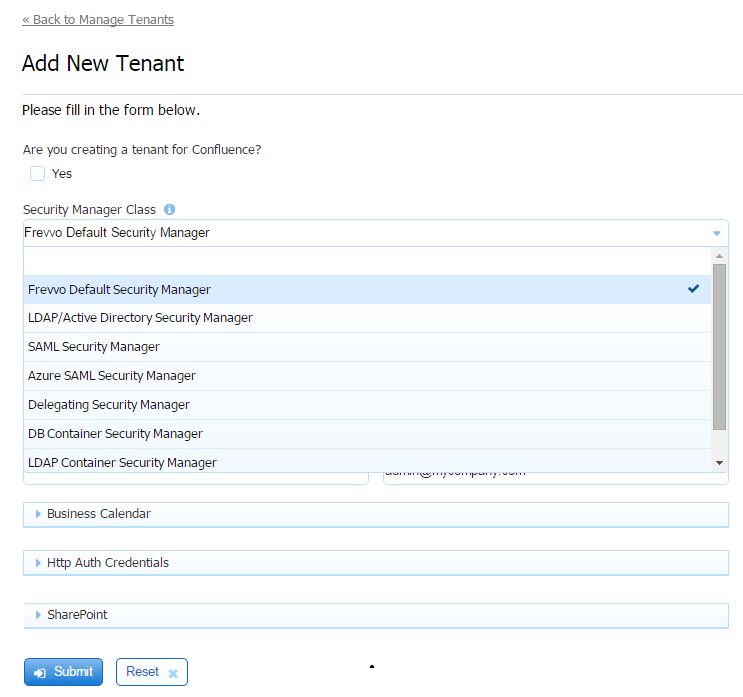
If you are not using Confluence, select a Security Manager Option from the following choices:
- Frevvo Default Security Manager (FSM) -
is responsible for authentication/authorization and managing users/roles. This is the default option. Your tenant will be created with this security manager if no other choice is selected.
- LDAP Active Directory Security Manager (LDAPSM) - The user is authenticated outside
. Typically, SSO or
performs the authentication using LDAP directly.
- SAML Security Manager - This security manager allows the exchange of authentication and authorization data between an identity provider of your choice (ex:Shiboleth) and a service provider (frevvo). SSO is supported. Although this security manager can be used on-premise it is primarily meant for cloud tenants who use LDAP but do not want to expose it over the internet.
- Azure SAML Security Manager - Allows the on-premises AD to be exposed to the cloud via synchronization with Azure AD. Uses the graph API to access users and groups from AD. SAML is used for authentication only, providing single sign on.
- LDAP Container Security Manager (LDAPCSM) - This is exactly the same as the DB Container Security Manager using LDAP/Active Directory instead of a database. Authentication is the container's responsibility.
- Custom - (CSM) - Container managed security manager used when there is a requirement for a container to handle authentication.
- Frevvo Default Security Manager (FSM) -
Tenant ID - Enter the tenant Id in this field - The tenant id can contain characters, numbers, dot(.), hyphen (-) and the underscore. It cannot start with a number. A common practice is to use your domain name for the tenant id.
- Tenant Name - Enter the name of the new tenant.
- Tenant Description - Enter a description for the new tenant.
- Max Concurrent Users - Leave this field blank if you do not want to set a maximum number of concurrent users. Concurrent Users are users that are logged into
simultaneously.
- Admin User Id - This is the tenant admin id. It can contain characters, numbers and the underscore. It cannot start with a number. The maximum length is 16 characters.
- Admin User Password - This is the tenant admin password. Notice the text will appear as bullets as you type.
- Reenter the Admin User Password - Reenter the tenant admin password.
will display an error message, "Invalid Value" if what you type in this field does not match the contents of the Admin User Password field.
Set Up the Business Calendar for your tenant
The superuser or tenant admin can set up the Business Calendar for your tenant. will then use the calendar information when calculating an escalation deadline for workflow steps and to determine the date/time for notification/reassign emails if they are configured. A tenant can only have one Business Calendar.
In the Business Calendar section of the Add/Edit Tenant screen:
- Select the timezone for your tenant from the dropdown. Escalation emails will display dates/times based on the selected timezone.
- Specify the working hours by entering a value in the Day Starts At and Day Ends At fields. The start and end hours are based on a 24 hr clock. Valid values are 0 - 23.
- Check the weekend days for your tenant.
- List the company holidays for the current year. You can specify holidays for future years as well.
The Business Calendar makes it very simple to configure workflow escalations based on a 5 - day work week. Once the calendar is set up, simply check the Business Calendar checkbox on the escalation condition in your workflow.
It is no longer necessary to use a rule to Calculate a Date based on a five day work week.
Configure HTTP Authorization Credentials
Live forms offers a user interface to specify credentials to external secure web services that are accessed by the forms/flows in your tenant. For example, if you have a rule that connects to a web service or a Form/Doc action that posts to a web service that is not publicly accessible, credentials can be configured for the services in each of your tenants.
The specification of http credentials for in-house customers was previously supported globally and configured in the httpclient-auth.properties file. This method is no longer used. In-house customers using this file for HTTP authentication should read the Migration Considerations before upgrading.
To configure http security credentials at the tenant level, follow these steps:
- The Http Auth Credentials section is at the bottom of the Edit/Add tenant screens and is initially collapsed. Click the icon to expand it.
- Enter the scheme from the dropdown. The admin may enter multiple credentials by clicking the icon. Each should be for a unique scheme/host/port/realm. The supported options are:
Basic - a common HTTP Authentication protocol that assumes that client credentials consist of a username and a password where the latter is a secret known only to you and the server
NTLM - a Windows network authentication protocol that allows a client to prove its identity without sending a password to the server.
Scheme, host, user name and password are required.
Port is optional and may be left blank. Either blank or -1 equates to any port and the system will alter blank to be -1.
All fields are specified in plain text and not encoded in any way.
Domain is only generally used for NTLM.
Configuring the SharePoint Connector
Store submissions and metadata on a registered SharePoint website using the frevvo SharePoint Connector and wizard. The configuration information is discussed in the SharePoint Connector topic
Configuring the LDAP/Active Directory Security Manager
Creating/editing the LDAP tenant is performed by the superuser (on-premise) or the tenant admin (cloud). Refer to this documentation for configuration details and here for some troubleshooting tips.
Configuring the LDAP Container Security Manager
There are some configuration items that must be performed before creating a tenant using the LDAPContainer Security Manager. Once the prerequisites have been completed, adding a tenant that uses the LDAP Container Security Manager is exactly the same as configuring a tenant using the LDAP/Active Directory Security Manager. Please follow the steps listed here.
Refer to the Configuring the LDAP Container Security Manager topic for the instructions.
Configuring the SAML Security Manager
Creating/editing the SAML tenant is performed by the superuser (on-premise) or the tenant admin (cloud). Refer to the SAML Security Manager topic for the details.
Configuring the Azure SAML Security Manager
Creating/editing the SAML tenant is performed by the superuser (on-premise) or the tenant admin (cloud). Refer to Configuring the Azure SAML Security Manager for the details.
Configuring the Database Container Security Manager
The Database Container Security Manager should be selected when authentication is the container's responsibility and you want to use the database interface to fetch users/roles for design time functionality from an external database. Click here for the /wiki/spaces/frevvo74/pages/355086544.
Edit Tenant
A tenant admin or a superuser admin can use the Tenant page to configure or edit information about a tenant.
To display the Tenant page:
- If logged in as a tenant admin click Edit Tenant.
- If logged in as a superuser admin click Manage Tenants and then click for the tenant you want to edit.
Note that you cannot change the Tenant Id, although you can change the Name and Description.
Change the tenant Security Manager
If you are planning on changing the Security Manager from the Default Security Manager to LDAP(s), SAML or Azure SAML, and you want to preserve Applications/Forms/Flows developed in your trial/starter frevvo tenant, here's what we recommend:
- Download the Applications/Forms/Flows that you want to preserve to your desktop as a backup BEFORE changing the Security Manager.
customers should be aware that changing the Security Manager of your tenant is a ONE-WAY operation. Once you click the Change button, you cannot revert back to the original security manager.
The following Security Manager changes can be made by clicking the Change button and making a selection from the dropdown. Cloud customers should contact sales@frevvo.com to initiate the procedure.
- Default Security Manager → LDAP
- Default Security Manager → SAML
- Default Security Manager → Azure SAML
- LDAP → SAML
- LDAP → Azure SAML
Click the button to see details about a field. Click Submit to save your changes. The message "Tenant updated successfully" will display.
Be aware that changing the Security Manager of your tenant is a ONE-WAY operation. Once completed, you CANNOT change it back to the original security manager.
Edit LDAP Properties
Edit SAML Properties
Edit Azure SAML Properties
Edit the Business Calendar
Changes to the Business Calendar can be made in the Business Calendar section:
Edit HTTP Authentication Credentials
Changes to the HTTP Authentication Credentials can be made by expanding the section:
Edit the SharePoint Configuration
Make changes to the SharePoint Connector in this section.
Email Address
The email address entered in this section is used as the from email address for email notifications and doc action emails for forms and workflows in the tenant. If you want to setup the email address with a user friendly name, enter the text in the Display Name field. The Document Action and Activity Document action email wizards have a From: address field. You can specify a different from email address for Document Actions and Activity Document action emails by entering a valid email address in the from field in both wizards. The values in these fields overrides the address entered on the Edit Tenant screen.
Refer to the Email configuration or integration topics for more information.
Session Timeout
A user designing a form, viewing their task list, or using a form to enter values and submit has a certain number of minutes to complete the activity. This time limit is called the Session Timeout. By default the session will expire after 30 minutes of inactivity. When the session expires a designer user will have to re-login to to continue designing forms and users filling forms will have to get new form instance and re-enter the values. The tenant admin can override the default session timeout with the value that is entered into the Session Timeout field.
Max Concurrent Users
The Max Concurrent Users field only appears if you are logged in as a superuser admin. This field enables you to restrict the number of users who can simultaneously login to a particular tenant. For example if you have purchased and installed a 20 user license key and want to set tenant A to use 5 and tenant B to use 15, setup that configuration here. See Concurrent Users for more information.
Max Users is subject to your license.
Deployment State
The Deployment State lets you toggle the default deployment state of your form between two states: PRODUCTION and DEVELOPMENT. When a form is in development state it contains a watermark. If you have a unlimited user license key you may want all the forms created by the designer to automatically be deployed for production with no water mark.
See also the deployment form property.
Anonymous Signup
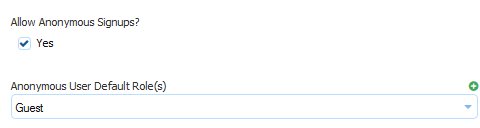
Anonymous signup lets you publish a registration Url for your tenant so people can signup and create a user account in your tenant themselves. In the Edit Tenant form, check the anonymous signup property and then select the default roles you want them to have when they signup. You can click the "+" to add multiple roles. If you select the designer role, these new users will have permission to design forms and workflows.
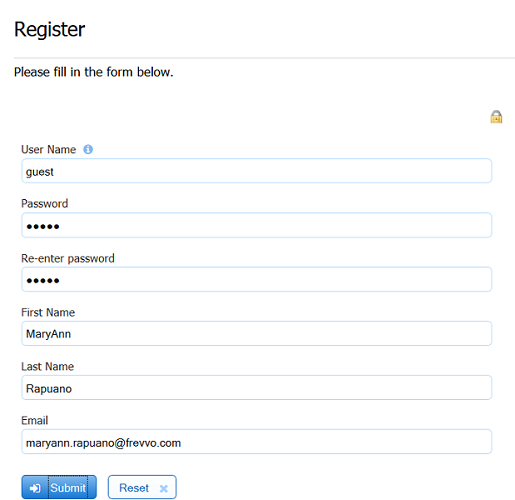
Then publish the registration Url:
https://www.frevvo.com/frevvo/web/tn/<your tenant name>/register?edit=true
At this Url people will see a signup form.
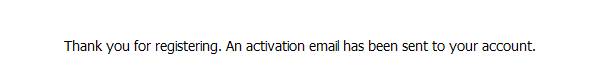
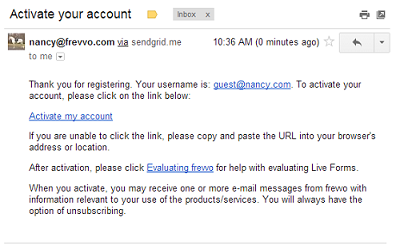
When they submit this form they'll be notified via email to activate their account. Until they activate via the email their account will remain disabled.
Now this person has a user account on your tenant and can login. If you gave them the designer role they will also be able to create forms and workflows. If not, when they login, they will see their task list as shown below.
Tenants configured with an LDAP or SAML Security Manager do not display the Anonymous Signup checkbox as this feature is not applicable for an LDAP or SAML tenant.
Tenant Setup
To setup your tenant, first login to your new tenant as the tenant admin. The tenant admin can add users to the tenant. You need to add at least one designer user in order to begin creating forms.
We strongly recommend that you do not use the admin user to create your own forms. You can create users and roles in your new tenant for that purpose.
- Click the Manage Roles link.
- You will see several pre-created roles: frevvo.Designer, frevvo.Editor, frevvo.Publisher, frevvo.ReadOnly.
- Click the icon, fill in the form and submit it to create new roles e.g. Employee or Manager.
- Click the Back to Manage Tenant link.
- Next click the Manage Users link.
- For
In-house you will see a single user – the administrative user you defined when you created the tenant. Note that you will have to click the link to display All users. By default, only users beginning with the later A are displayed. For
Online you will see two users – the administrative user and the designer username you specified when you signed up for your trial SaaS account.
- To create a new user with permissions to create forms, click the icon, fill in the form and select the role frevvo.designer. If you do not select this role then this new user will not be able to create forms but will only be able to use forms created by others.
- The new user will be created. Create as many users and assign them roles as needed.
- Logout of the tenant admin account and login as one of the newly created users with the frevvo.Designer role and start building forms and workflows.
- Note that you must login using either the syntax: userid@tenant for the user name. For example, if the newly created tenant was named example.com then all users in that tenant must login using the ID: user@example.com. If you prefer to enter the username and tenant name in their own login page input fields, the configuration parameter, frevvo.login.show.tenant, can be modified to display the tenant name input field.
Related Topics
https://frevvoit.atlassian.net/browse/TIP-21206