This documentation is for Live Forms 9.1. v9.1 is a Cloud Only release. Not for you? Earlier documentation is available too.
COVID-19 Response Info: At frevvo, our top priorities have always been employees and customers. We have taken several steps to promote the well-being of our people, to minimize services disruptions, and to help where we can. Visit our website for updates.
SAML Security Manager
supports the creation of a tenant using the SAML (Security Assertion Markup Language) Security Manager. Users in this tenant can log into
via (SAML) version 2.0. SAML enables internet single sign-on by allowing users to authenticate at an identity provider and then access service providers without additional authentication.
The SAML Security manager can be used in on-premise installations but it is primarily meant for cloud tenants who use LDAP but do not want to expose it over the internet.
SAML requires the configuration and installation of an identify provider that supports SAML 2.0. Some examples are Google, Shibboleth, OpenSSO, ADFS, and PingFederate, OneLogin.
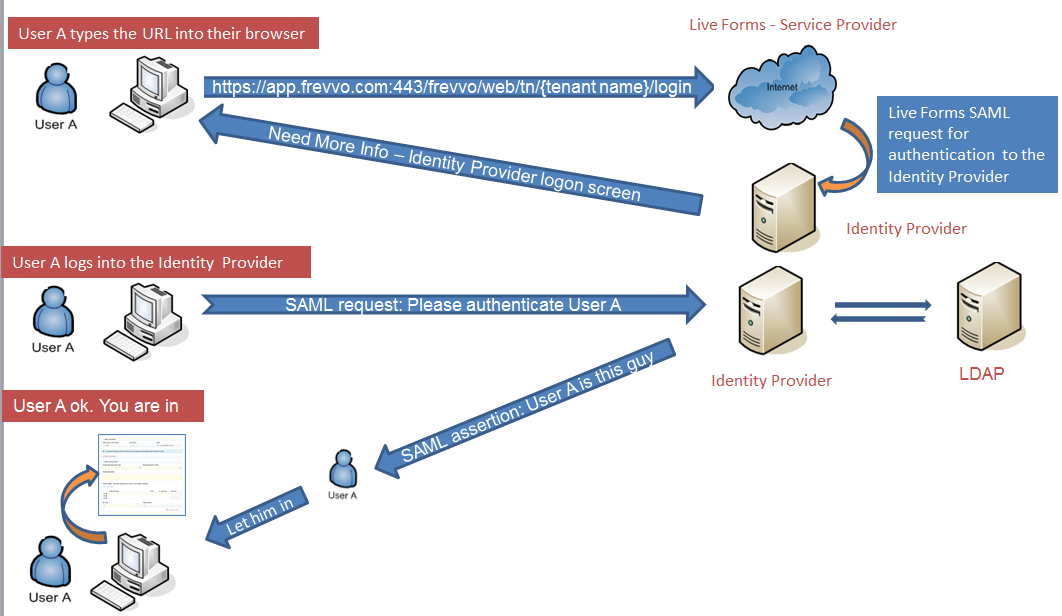
In a SAMLenvironment, integration with an LDAP server for authentication is common. In general, here's how it works:
- User A attempts to access Live forms by typing the URL into the browser
- Live forms sends a SAML request for authentication to the Identity Provider
- The Identity Provider requires more information. The Identify Provider login screen is displayed.
- User A logs into the Identity Provider.
- The Identity Provider may communicate with your LDAP server if you are using Active Directory for authentication.
- The Identity Provider builds and sends a SAML token to Live Forms containing the security information for User A.
- Live forms processes the information. If User A has been authenticated, Live forms establishes a session and redirects User A to the correct Live Forms screen depending on User A's authorization level.
On this page:
frevvo only supports/certifies the SAML Security Manager when is running in the tomcat container. Refer to our Supported Platforms for the list of Application Servers supported/certified by frevvo.
Prerequisites
Authentication Only mode:
When you create your SAML tenant, you can select Authentication Only mode..This is done by checking a checkbox when you configure your SAML tenant.
If Authentication Only is selected, SAML is used only for authentication. Authorization depends on the roles defined in . SAML will authenticate the user but not retrieve any of the attributes.
You may choose to use this mode if you:
do not want to add
roles to your LDAP.
LDAP has many roles that have no relevance to your workflow.
Find the SAML mapping for the other required attributes complex. For example, retrieving the manager user id and role names may require writing custom rules.
In this mode, manual creation of users & roles in the tenant is required. The
CSV upload feature makes this easy.
If Authentication Only is not selected, users will be added (discovery) at runtime when they log in for the first time. It is important to consider the following points before making your decision.
User discovery:
There is no guarantee that the first login will occur before a task is created for a specific user /role. If you have workflows, that are routed to users who have not logged in yet, your workflow may not do what you expect. If the user’s role changes after 1st login but before the next task is routed to their new role, the task will not appear on their Task List. For example, a user with the role of employee, logs into
. The user then gets promoted to manager. The user will not receive a task routed to the user's new role of manager if the workflow is initiated before the user logs out and logs in again and the user account is updated.
Manually creating/uploading users and roles ahead of time avoids this situation.
- Active Directory:
- Customers using LDAP must ensure that the frevvo.User, frevvo.TenantAdmin and frevvo.Designer roles are specified on their LDAP/AD server.
- All users requiring access to
must be assigned to the frevvo.User group.
- Tenant admin users must be assigned to the frevvo.User and frevvo.TenantAdmin groups,
- Designer users must be assigned to the frevvo.User and frevvo.Designer groups.
- All users requiring access to
- Customers using LDAP must ensure that the frevvo.User, frevvo.TenantAdmin and frevvo.Designer roles are specified on their LDAP/AD server.
- The group names for these three special roles must be frevvo.User, frevvo.TenantAdmin, and frevvo.Designer. Upper/lower case may be a factor for Open LDAP systems.
- frevvo Best Practice recommends that you create a user account in your Active Directory or IDP that will house all of your deployed Production forms/workflows. This user can be named anything i.e.frevvoProduction but it must be a member of the frevvo.Designer group
- If you want to preserve Projects/Forms/Workflows developed in your trial/starter tenant, download them to your desktop as a backup BEFORE changing the Security Manager
- frevvo only supports the SAML Security Manager when
is running in the tomcat container. Refer to our Supported Platforms for the list of Application Servers supported/certified by frevvo.
Configuring the SAML Security Manager
In the directions given below, the Service Provider refers to frevvo . The metadata for your
SAML tenant must be obtained first. Customers will need to configure the
metadata when creating the SAML tenant.
- In-house Customers Only
- Create the frevvo Metadata file.
- Configure your Identity Provider
- Create/edit the SAML tenant
- Manage Users/Roles for your SAML tenant
- Logging into Live Forms in a SAML Tenant
Section 1 - In-house Customers Only
Cloud customers can skip the Generate Your Certificate and Install the Java Cryptography steps. These instructions are provided for On-premise customers only.
Generate Your Certificate
If you re using the frevvo tomcat bundle, the supplied keystore, frevvoKeystore.jks is located in the <frevvo-home>/tomcat/lib folder, The keystore contains a default certificate. Replace this with a certificate for your installation.
This certificate is used to sign/encrypt the SAML request. The use of a long-lived self-signed certificate for SAML is recommended because a CA certificate is usually only valid for 1 to 2 years and you have to keep replacing it. Since the keystore is located outside the frevvo war, you can use the Java keytool to generate and store your certificates
The alias, password and path to the keystore are configured in the <frevvo-home>\tomcat\bin\setenv.bat and the service.bat files for the Windows OS or setenv.sh for UNIX/Linux OS. The properties listed below are used in the setenv and service.bat files to set the default values:
- com.frevvo.security.saml.key - use this property to change the alias
- com.frevvo.security.saml.password - use this property to change the password
- com.frevvo.security.saml.keystore - use this property to change the location of the keystore
rem SAML keystore configuration
set CATALINA_OPTS=%CATALINA_OPTS% -Dcom.frevvo.security.saml.keystore=file:${catalina.home}/lib/frevvoKeystore.jks -Dcom.frevvo.security.saml.key=frevvo -Dcom.frevvo.security.saml.password=p@ssw0rd
# SAML keystore configuration
export CATALINA_OPTS="${CATALINA_OPTS} -Dcom.frevvo.security.saml.keystore='file://${CATALINA_BASE}/lib/frevvoKeystore.jks' -Dcom.frevvo.security.saml.key=frevvo -Dcom.frevvo.security.saml.password=p@ssw0rd"
set SAML_ARGS=-Dcom.frevvo.security.saml.keystore=file:${catalina.home}/lib/frevvoKeystore.jks;-Dcom.frevvo.security.saml.key=frevvo;-Dcom.frevvo.security.saml.password=p@ssw0rd
Follow these steps to generate and import the certificate for your installation:
- Stop
if it is running.
- Copy the default <frevvo-home>\tomcat\lib\ frevvoKeystore.jks to another location as a backup
- Login as administrator.
- Make sure the path to the keytool application is configured in your system path. keytool is part of the standard Java distribution (JDK or JRE)). For example, keytool is located in the C:\Program Files\Java\jdkx.x.x\bin directory in the JDK.
- Navigate to <frevvo-home>\ tomcat\lib or to the new location of the keystore if you changed the com.frevvo.security.saml.keystore property in the setenv or service.bat files
Delete the existing certificate:
keytool -delete -alias frevvo -keypass p@ssw0rd -keystore frevvoKeystore.jks -storepass p@ssw0rd
If you changed the password from the default, execute this keytool command to change the password in the keystore
keytool -storepasswd -keystore frevvoKeystore.jks - it will ask for the old password - p@ssw0rd and then prompt for the new one - The keystore password must match whatever is in the line that we added to the setenv pr service.bat files.
Generate a new certificate: Here is the command: Change the -dname value to the DNS name of your IDP.
If you changed the values of the com.frevvo.security.saml.key or com.frevvo.security.saml.password properties in the setenv or service.bat files then change the alias in the command and the keypass and storepass password parameters to match those values. The key and store passwords need to be the same as there is only one password property.
The dname in this keytool command specifies the X.500 Distinguished Name to be associated with the alias and is used as the issuer and subject fields in the self-signed certificate. While we provide a sample in the documentation, it is up to the customer (your security policy) to decide what the value should be when the certificate.for your installation is generated. Since this is a self-signed certificate - the dname really could be anything - but here is a link to the Oracle documentation to give you some idea of what you might want to set that too.
Execute this command to create a new certificate and stores it in the keystore.keytool -genkey -dname "cn=app.frevvo.com" -alias frevvo -keypass p@ssw0rd -keystore frevvoKeystore.jks -storepass p@ssw0rd -keyalg rsa -keysize 2048 -validity 3650
The certificate can be viewed by exporting it to a file. If you changed the password, substitute the new password in the command:
keytool -exportcert -alias frevvo -file frevvo.rfc -rfc -keystore frevvoKeystore.jks -storepass p@ssw0rd
Install the Java Cryptography Extension
The Java Cryptography Extension (JCE) provides a uniform framework for the implementation of security features in Java. These files are needed to avoid an "illegal key size" error which can happen if these files are missing in the Java Development Kit (JDK) software of your on-premise installation.
Determine the version of the Java 8 JDK that you are running by typing java -version in a command window
- If you are using a version of the JDK 8 u161+ , you can skip this step.The correct jar files are already included in the JDK.
- For versions of the JDK 8 previous to u161, follow these steps to install the JCE files into the JDK:
- Go to the Oracle Java SE download page.
- Scroll down … Under "Additional Resources" section you will find "Java Cryptography Extension (JCE) Unlimited Strength Jurisdiction Policy File"
- Download the version that matches your installed JVM - for example, download UnlimitedJCEPolicyJDK8.zip if you are using JDK/JRE version 8
- Unzip the downloaded zip.
- Copy local_policy.jar and US_export_policy.jar to <JAVA_HOME>/jre/lib/security (Note: these jars are already there so you have to overwrite them)
- Restart
.
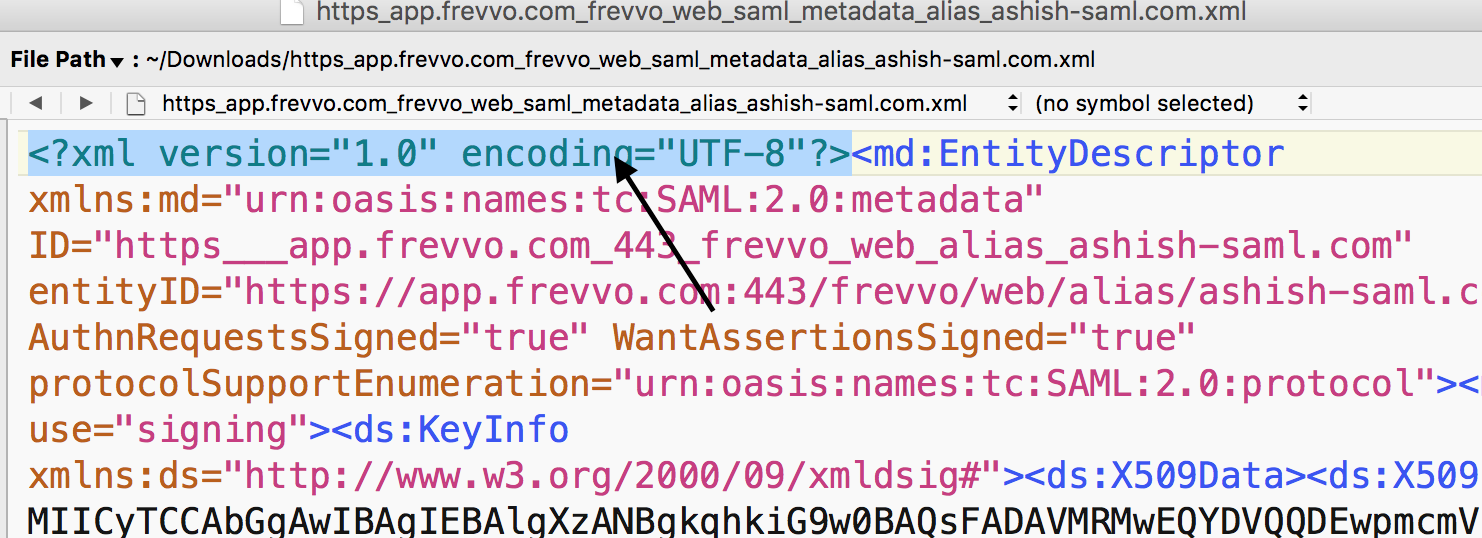
Section 2 - Create the Live Forms Metadata file
Follow these steps to generate the frevvo metadata for your SAML tenant. You can do this even if the tenant has not been created yet.
Paste this URL into your browser:
Cloud Customers: https://app.frevvo.com:443/frevvo/web/saml/metadata/alias/{t} - replace {t} with the tenant id of your SAML tenant.
On-premise customers: http://<server>:<port>/frevvo/web/saml/metadata/alias/{t} - replace <server> with the ip of your server, <port> with the port number (if applicable) and t with your tenant id).
When the metadata displays, right click and select the browser option to View the Page source.
- Save the page as an xml file.
- Metadata must be generated for each SAML tenant. Each tenant will have a unique URL.
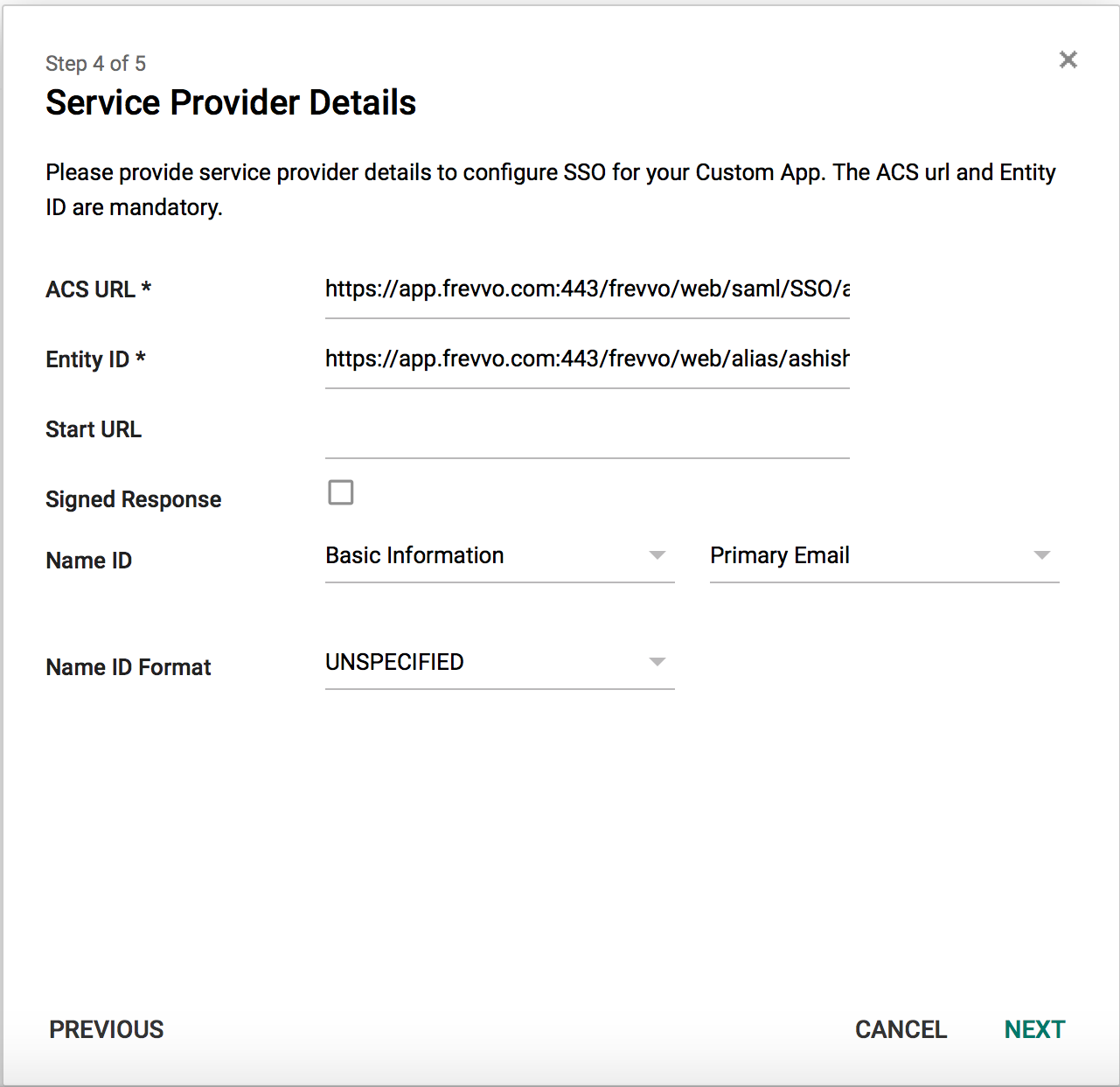
Section 3 - Configure Your Identity Provider
- Configure the Service Provider metadata for your Identity Provider. For example, the Shiboleth Identity provider requires modification of a file to provide the path to the
tenant metadata xml file created above.
- Your Identity Provider must be configured to expose the attributes that
requires. Attribute mapping is done when you create the SAML tenant. These are:
- User Id
- First Name
- Last Name
- Manager Id (optional)
- Groups
- Custom Attributes (optional)
We know that your IDP software of choice is outside of the frevvo server software and that you have the expertise in house to install, configure and maintain your IDP software. But here are some tips we have found that may assist you.
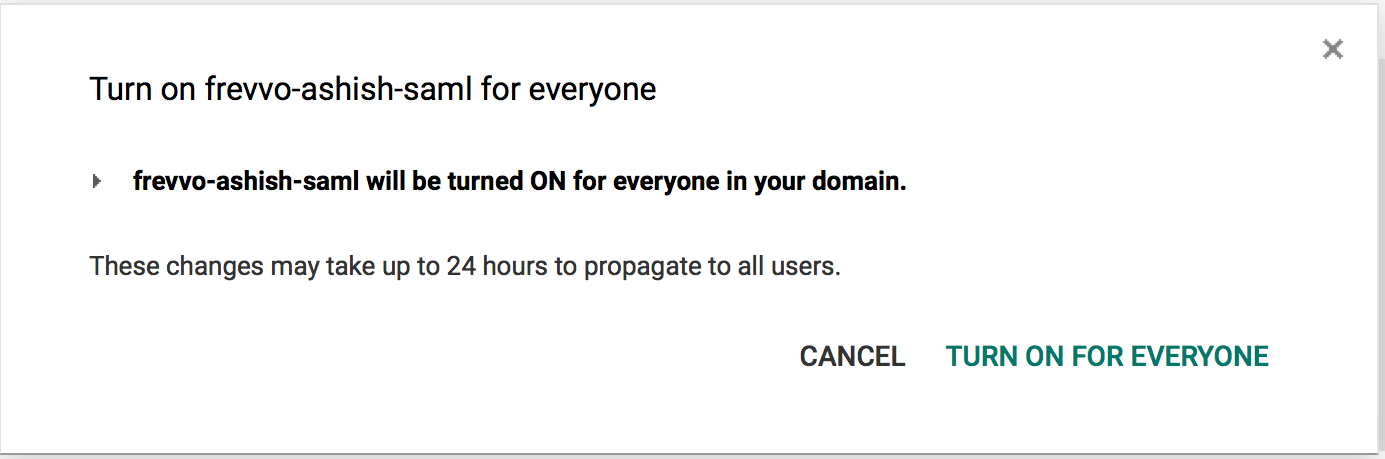
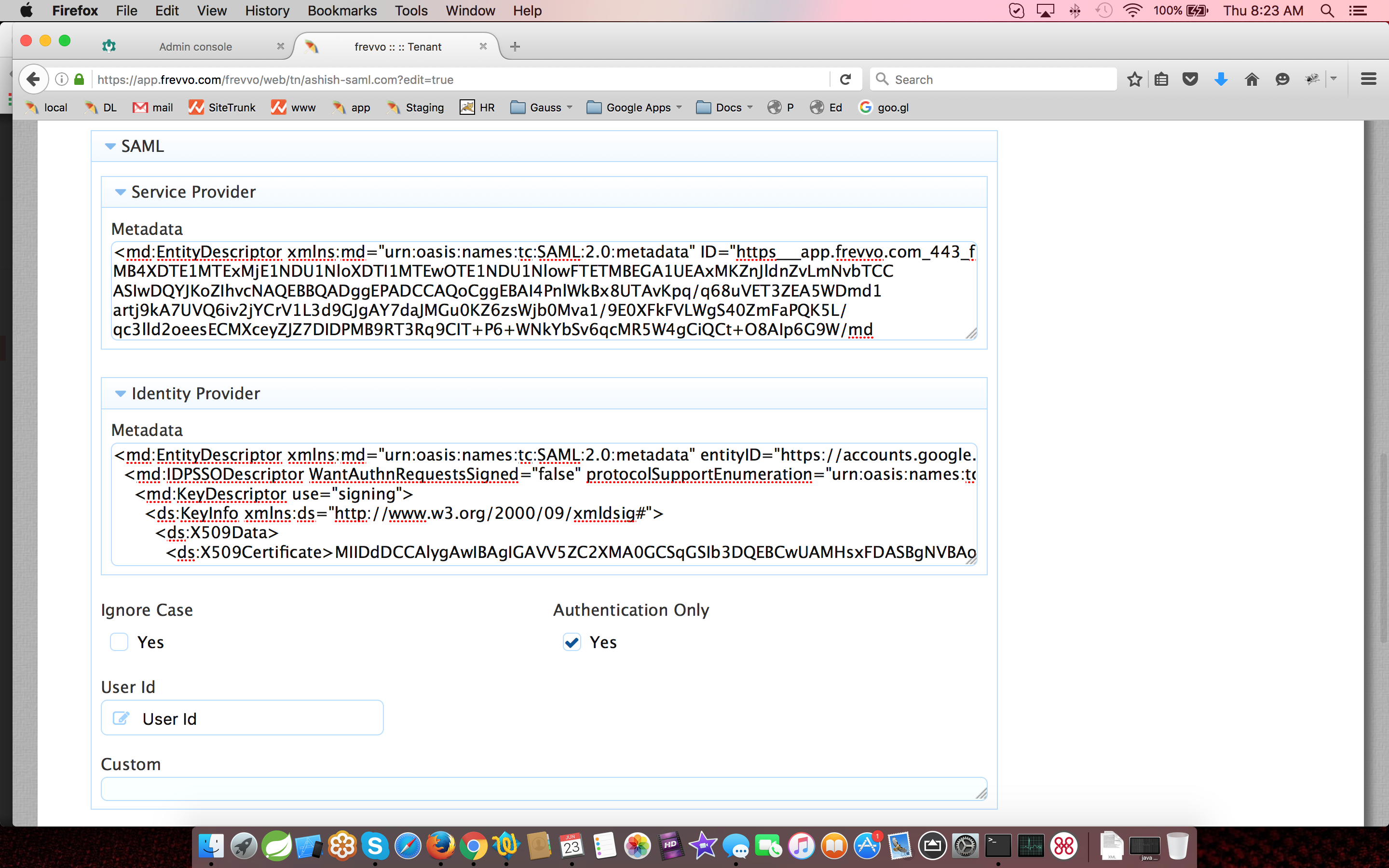
Section 4 - Create or edit the SAML tenant
To successfully create a tenant using the SAML Security manager, you will need the following:
- The metadata for your Identity Provider
- Attribute mapping information
cloud customers, migrating your tenant to the SAML Security Manager, will make the changes via the Edit Tenant screen. Once accessed, follow these steps beginning with step 2.
Log onto as the superuser (on-premise) or the tenant admin (cloud).
- Access the Add Tenant (on-premise) or Edit Tenant (cloud) screen.
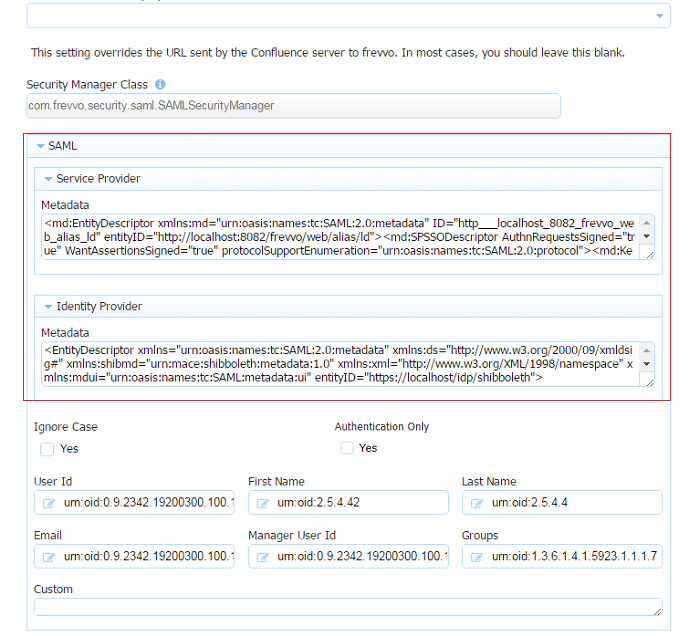
- Select SAML Security Manager from the Security Manager Class dropdown.
- Copy the Service Provider (frevvo) metadata into the Service Provider field. The xml should be pasted without the prolog. For example, the image shows an example of the frevvo metadata file before pasting:
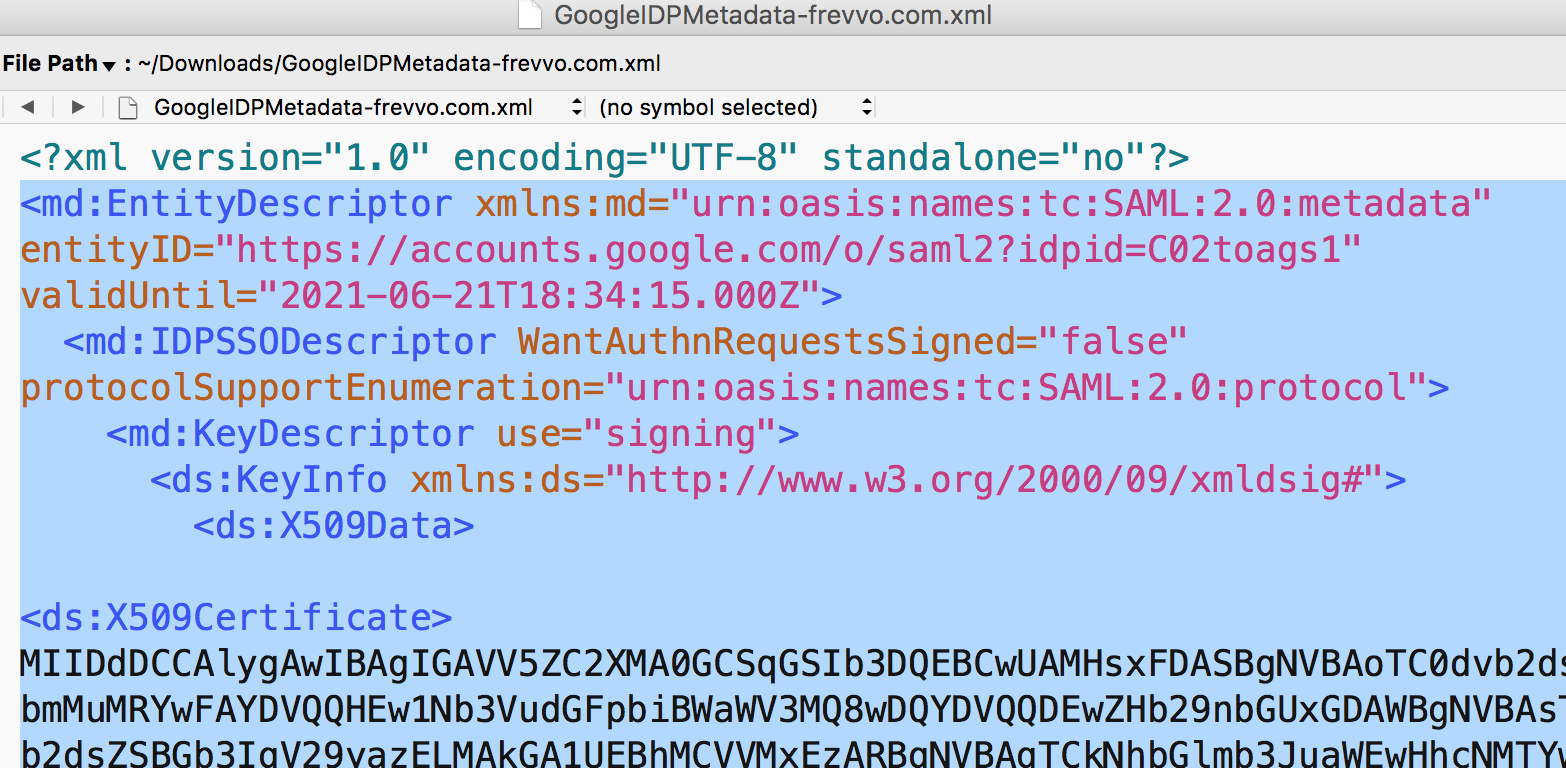
- Retrieve the metadata for your Identity Provider. For example, for the Shiboleth product the metadata is located in the idp-metadata file.
- Paste the metadata into the Identity Provider field. This metadata should also be pasted without the prolog.
- Check the Ignore Case checkbox if you are using LDAP for authentication and you want
to ignore the case stored in LDAP systems for users/roles. It is checked by default. Refer to the /wiki/spaces/frevvo91/pages/901492728 topic for more information.
Check the Authentication Only checkbox if you want SAML to handle authentication and provide user identification but all other user attributes come from the
database.
When checked, the screen display changes as attribute mapping, other than the mapping for the user id and custom attributes, is no longer necessary.- If Authentication Only is checked:
- SAML will authenticate the user but not retrieve any of the attributes. Authorization depends on the roles defined in
. Changes made in the
UI will not be overridden if the user logs out and then logs in again.
- Manual creation of users & roles in the
SAML tenant is required. This can be done with a csv upload.
- SAML will authenticate the user but not retrieve any of the attributes. Authorization depends on the roles defined in
- If Authentication Only is unchecked:
All users requiring access to
must be assigned to the frevvo.User group in Active Directory. Tenant Admins must be assigned to the frevvo.User and frevvo.TenantAdmin groups. Designer users must be assigned to the frevvo.User and frevvo.Designer groups.
- Users are added (discovered) when they log in.
- It is important to know that a SAML tenant in this mode (SAML/LDAP handles authentication and authorization) that users and tenant admins can modify user information in the
UI. If user information/role assignment is changed in the
UI, the changes will be overwritten by the information in SAML the next time the user logs out and then logs back in again. In this case, make the changes in your Active Directory to make them permanent.
- If Authentication Only is checked:
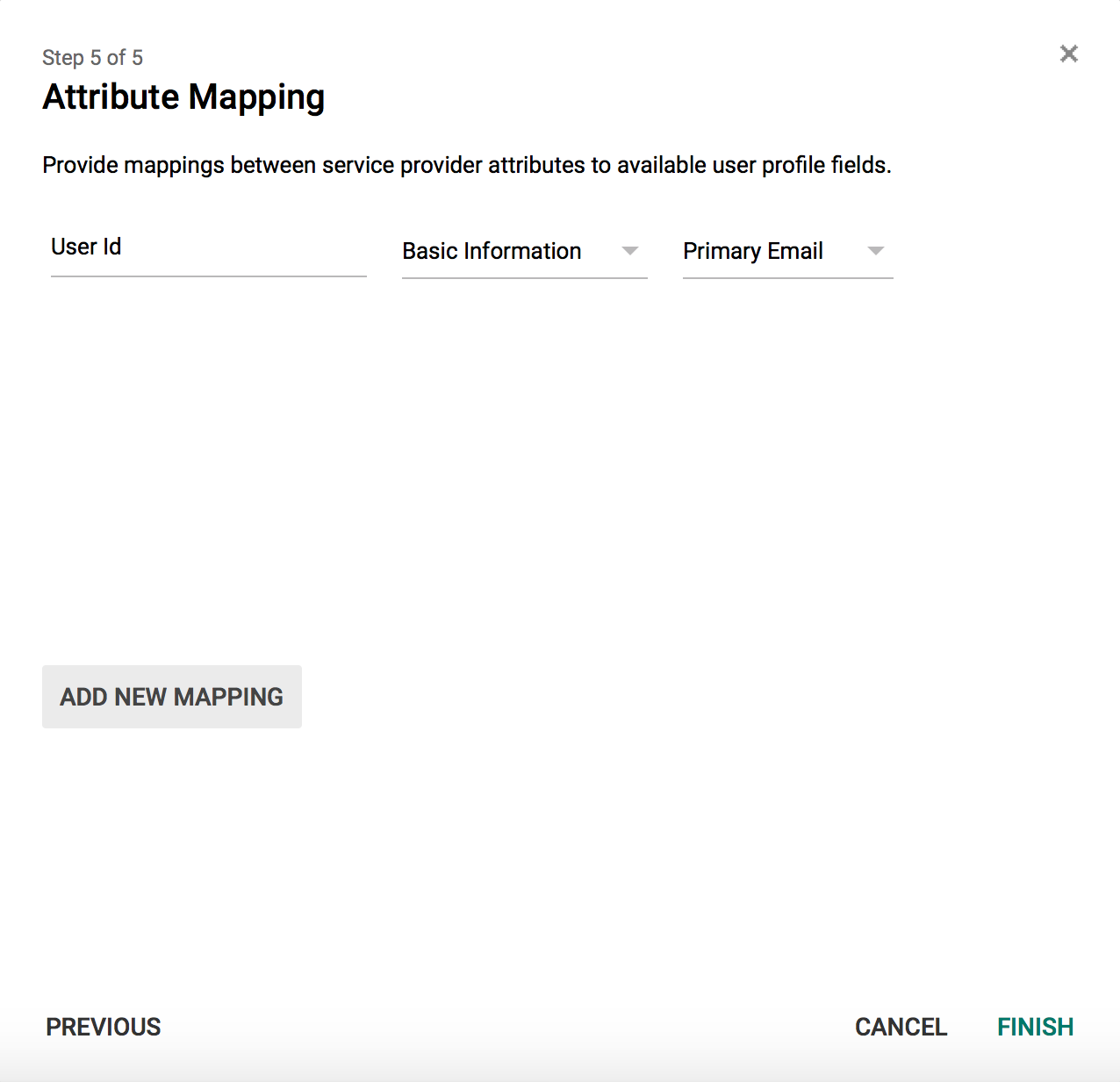
Map the attributes configured in your Identity Provider by entering the name for each attribute in the corresponding field on the
screen. Be sure to provide the attribute name - not the friendly name. For example, if you are using Shibboleth for your Identity Provider the attribute information is located in the attribute-resolver.xml file. The image shows the section of the file where the attributes are defined.
The image below shows the attribute mapping on thescreen with the attribute names from the Shibboleth file:
If Authentication Only mode is enabled for your tenant, mapping is only required for the User Id. Refer to step 8 for the details
- Custom attributes can be mapped by typing the attribute names in the Custom field separated by a comma.
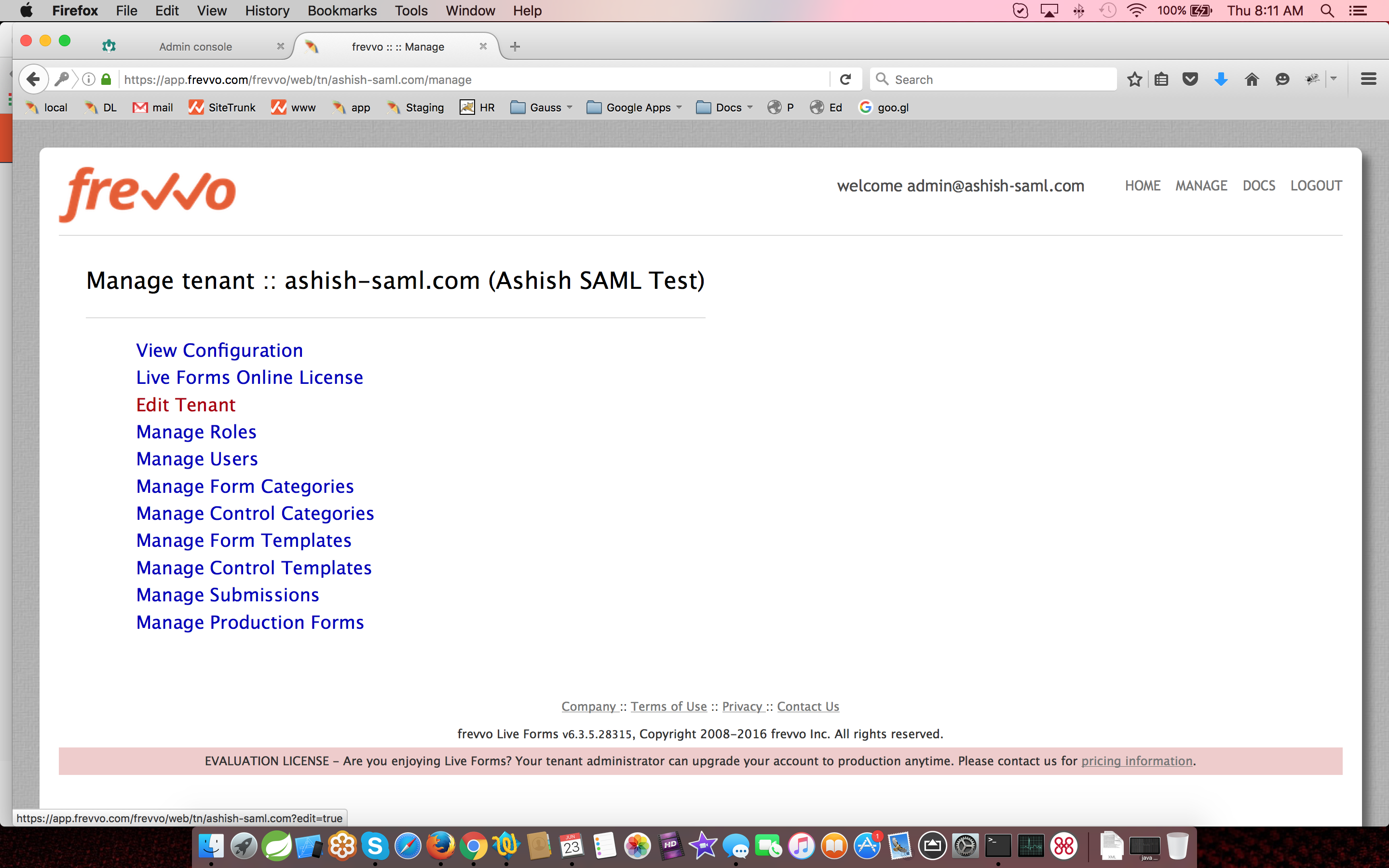
- Configure a tenant admin account. This account does not require SAML authentication. This tenant admin can log directly into
.
- The tenant admin id, password and email fields are required. The Change password on next login field is optional. It is checked by default.
- When this tenant admin performs a form based login i.e. /frevvo/web/login, the password entered on this screen is used for authentication. This is also the URL used by the API. For cloud customers the <base> is always https://app.frevvo.com.
- If the tenant based login url is used i.e. /frevvo/web/tn/{t}/login then SAML login is used.
The forgot password function works for a SAML tenant admin user. For all others, it will display the error message about not being supported for the tenant. - Configure the Business Calendar for your tenant and HTTP Authorization Credentials if required.
- Click Submit.
Section 5 - Users and Roles in a SAML tenant
Choosing the Authentication only option in your SAML tenant implies that the user and roles will be managed from . You may choose this mode if:
- You do not want to add
roles to your LDAP.
- LDAP has many roles that have no relevance to your workflow.
- Find the SAML mapping for the other required attributes complex. For some IDPs, retrieving the manager user id and role names may require writing custom rules.
- You do not want to add
When Authentication Only is selected (checked) there is no discovery of Users & Roles. They must be created in your tenant manually. The CSV upload is a good way to do this.
When Authentication Only is not selected (unchecked) will discover new users at run-time. However users are only discovered when the person tries to login. They are not discovered nor is their user data (email, name, report-to) kept in sync automatically. It requires the user to login. So, this does not necessarily remove the need for manually creating/uploading users and roles ahead of time nor does it remove the need to continuously update the users when changes are made in LDAP.
If you have workflows that are routed to users/roles there is no guarantee that the required users will login before a task is created for that user (specifically or via a role). For example, if a workflow is routed to a specific user and it is performed before the first login of that user, will send an email to the tenant admin indicating that the user is unknown. Routing based on the user's manager will fail. Routing based on a role will succeed but the user will receive no notification.
Manually creating/uploading users/roles in ahead of time avoids this situation.
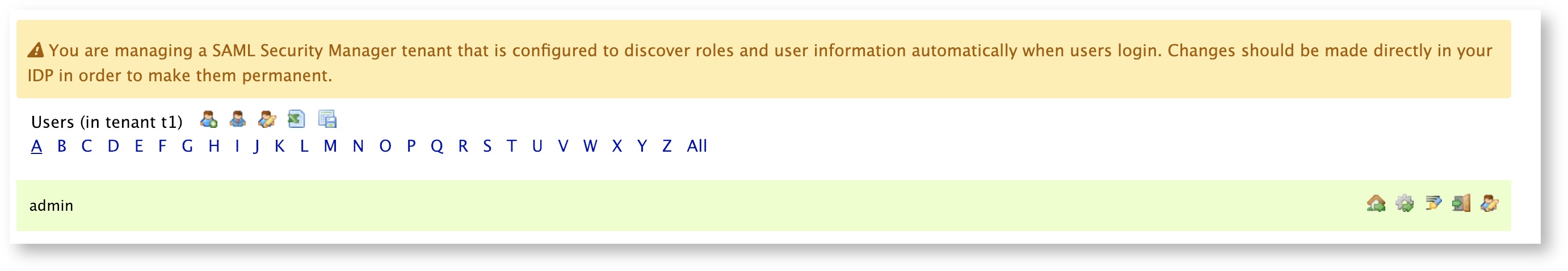
It is important to know that a SAML tenant with Authentication Only unchecked, means that authentication and authorization are handled by SAML/LDAP. Users are added/updated through discovery. If a tenant admin modifies user information in the UI, for example, changes an email address or adds a role for a user, the changes will stay in effect until the user logs out of the tenant and then logs back in. When the user logs back in, the changes made in the
UI will be overwritten by the information in SAML/LDAP. In this case, make the changes in your Active Directory to make them permanent. A warning message will appear on the User List to alert the admin that they are in discovery mode and should make permanent changes in their IDP instead.
Discovery updates only occur when the user logs into the tenant. The admin "login as" feature will not execute a discovery update.
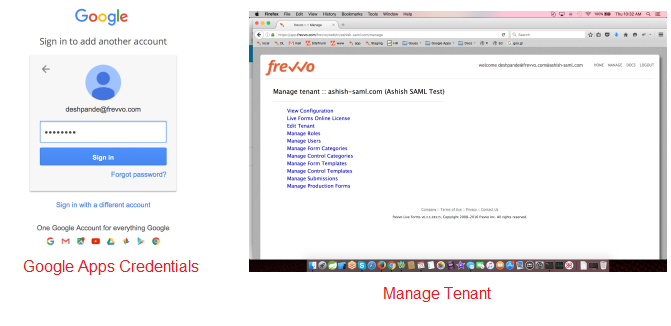
Section 6 - Logging into a Live Forms SAML Tenant
Browse the URL below to initiate the SAML authentication process by redirecting to the Identity Provider login page.
Cloud Customers: https://app.frevvo.com:443/frevvo/web/tn/{t}/login. Replace {t} with the name of your SAML tenant.
- On-premise Customers: http://<server>:<port>/frevvo/web/tn/{t}/login. Replace <server> and <port> with your server information and t with the name of your SAML tenant.
- Clicking the logout link in
, logs the user out from
only.
- Accessing a Space in a SAML tenant on a mobile device will not display a logout button.
- When a user logs in to Live Forms (non-space mode), the logout link will be visible
- Cloud customers browsing app.frevvo.com or in-house customers browsing http://<servername>:<port>/frevvo/web/login attempting to log into a SAML tenant directly (user@saml tenant name) will automatically be redirected to the SAML IDP login page. For best performance, frevvo recommends using the login URL described above.
SAML Tenant Built-in Admin User
Just a reminder that the tenant admin account can login directly into Live Forms or use the SAML login.
When you create/edit a new tenant you are prompted to set up/modify a tenant admin user id, password and email address. This tenant admin does not authenticate via your SAML IDP. It only exists in Live Forms. If you experience an issue with your SAML configuration such that you can't login as an SAML authenticated user, use the built-in admin to login to your tenant as a tenant admin in order to fix your SAML configuration issue. Only one built-in tenant admin account is supported.
Browse this URL to login as the built-in: <base_URL>/frevvo/web/admin/login. When specified, will prepend the base URL to the URLs in your Form/Document Actions. The <base_URL> is typically http(s)://<your servername>:<port>.
- You must use the admin specific URL - <base-url>/frevvo/web/admin/login - to login as the built-in.
- Non admin users can also login using the admin specific URL.
If your tenant originally used the Default Security Manager and then you changed to the SAML Security Manager, this tenant admin account has already been setup. If you have forgotten the password, you can change it by:
- Browsing the admin specific URL - <base-url>/frevvo/web/admin/login. Enter the built-in userid. Click Forgot Password? This error message displays if any other user clicks on the Forgot Password? link after browsing the admin specific URL:
- Logging in as a SAML authenticated tenant admin and changing the password via Manage Users.
The frevvo superuser admin (Cloud customers) and the in-house superuser can change the password for the built-in userid from the Edit Tenant page.
What if you do not remember the userid of your original tenant admin? Follow these steps:
- Login as your authenticated Azure SAML tenant admin
- Click Manage Users and click the edit admin icon
The frevvo (Cloud customers) and in-house superuser can see the built-in tenant userid from the Edit Tenant page.
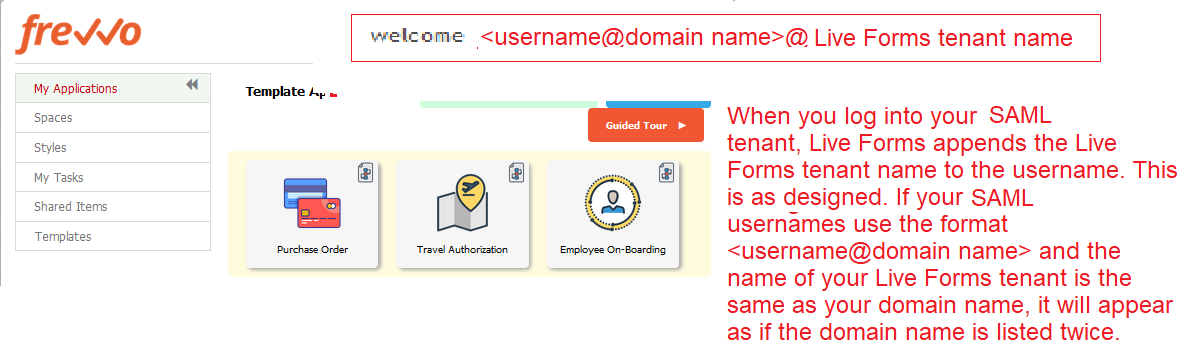
Logged in User Display in Azure SAML Live Forms tenant
If your SAML userIds are in the format <username>@<domain name>, when you login to the
tenant name is appended to the userId . This is as designed. You will see <username@domain name@frevvo tenant name> as the logged in user at the top of the screen. If your domain name is the same as your
tenant name, it will appear as if the domain name is listed twice.
Session Timeout
Session timeouts are configured in and in your IDP. If a user's session ends before the IDP timeout is reached, they will automatically be logged back into
if they try to access it again. It is recommended that the
session timeout and the IDP session timeout be configured for the same value.
Embedding Forms/Workflows in your website
Embedding forms and workflows into your website when using the SAML Security Manager, will work in the following scenarios :
- The visibility of the form is set to Public.
- The visibility of the form is set to Public in Tenant and the user is already authenticated to SAML
Embedding forms and workflows into your website (and other use of the Link (Email/Webpage) share URL) is NOT supported if the the visibility of the form is set to Public in Tenant and the user is NOT already authenticated to SAML. This is because frevvo must direct the user to the IDP login screen and the browser will not allow loading the IDP login page in frevvo's form iframe. Users will see an error like this one if you open your browser's console:
Refused to display 'https://....' in a frame because it set 'X-Frame-Options' to 'deny'.
If the tenant is using a SAML security manager, always use the Raw form link (see this documentation) to access your forms. This link will not load the form in a frame and login will work as expected.
If you are embedding your forms inside another website, then make certain that user has to login to IDP before they can see that web page. If the user is already logged in, the form will load correctly (even inside a frame).
Automating the Daily CSV Upload
Customer's using the SAML Security Manager, often want to schedule a daily upload batch job to automatically handle the synchronization between their Active Directory and . The Java Client API is one way to do this. Refer to the How do I batch upload users from the api? topic for the details.
Retrieving Custom Attributes from LDAP in a SAML Tenant
Similar to the LDAP Security Manager, custom properties in Active Directory for the logged in user can be made available so you can pull them into your form/workflow using a business rule. Attributes have to be configured and released in your IDP configuration for them to be available on login.There are several steps that have to happen to accomplish this:
- Make sure Authentication Only is unchecked in your SAML tenant.
- Make sure the custom attribute(s) are configured in Active Directory and assigned to the correct users.
Configure and release the custom attributes as SAML attributes in your IDP.
The procedure to expose custom attributes will differ depending on the IDP you have selected. Refer to your IDP documentation or your on-staff IDP expert to complete this step.
- Map the attribute with this name in the Custom section of the tenant setup screen.
- You can do this when you are creating your SAML tenant or by accessing the Edit Tenant link, after signing on as the tenant admin of your existing SAML tenant.
- Save the tenant configuration.
- Write a
business rule to populate controls in your form/workflow with the information.
Example:
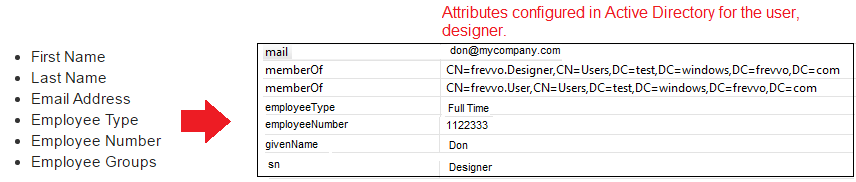
Let's take a look at a installation using a SAML tenant, Shibboleth as the IDP and Active Directory for authentication. When the user logs into the SAML tenant, you want to populate these fields in your form with the information from the LDAP server:
These attributes must be configured and released in your IDP. The process to expose the attributes varies for each Identity Provider. In our example, which uses the Shibboleth IDP, configuration and release of the attributes is done in two files, attribute-resolver.xml and attribute-filter.xml. You may need to confer with your on-staff IDP expert to complete this step.
Here is an example of the section of the attribute-resolver.xml file that was added to for the employeeType and employeeNumber custom attributes:
When the attributes are configured in the IDP, add them to the Custom section for attribute mapping by editing/creating your SAML tenant :
Note the friendly name for the employeeType is listed here while the name of the employeeNumber attribute is used. This was done to match the configuration of the attributes in the IDP.
Next, create your form with fields to collect the attribute information. Include a Dropdown control that will be populated with the groups (roles) that are assigned to the designer user in Active Directory. Add a rule to pull the information into your form:
if(form.load) {
FirstName.value = _data.getParameter('subject.first.name');
LastName.value = _data.getParameter('subject.last.name');
EMail.value = _data.getParameter('subject.email');
EmployeeType.value = _data.getParameter('subject.employeeType');
EmployeeNumber.value = _data.getParameter('subject.urn:oid:0.9.2342.19200300.100.1.30');
MemberOf.options =JSON.parse(_data.getParameter('subject.urn:oid:1.3.6.1.4.1.5923.1.1.1.7'));
}
Troubleshooting Tips
Login fails with illegal Key Size Error
After a failed login, if this error message appears in the <frevvo-home>\tomcat\logs\frevvo.log file:
org.apache.xml.security.encryption.XMLEncryptionException: Illegal key size at org.apache.xml.security.encryption.XMLCipher.decryptToByteArray(XMLCipher.java:1822) ~[xmlsec-1.5.7.jar:1.5.7] … org.opensaml.xml.encryption.DecryptionException?: Failed to decrypt EncryptedData? at org.opensaml.xml.encryption.Decrypter.decryptDataToDOM(Decrypter.java:546) ~[xmltooling-1.4.4.jar:na] …
Solution:
This error indicates the Java Cryptography Extension (JCE) Unlimited Strength Jurisdiction Policy Files are missing in the Java Development Kit (JDK) software of your on-premise installation. Esnure you have the support version of JDK installed which includes the JCE.
The IDP login page does not display in the Microsoft Edge Browser
In-house customers may see a blank page may see a blank page when browsing the URL to access your SAML tenant in the Microsoft Edge browser. There is a known issue with the Edge browser and untrusted self signed certificates especially where redirect is concerned. Registering the certificates in Windows will not work. The workaround is to:
- Refresh the page. It shows the untrusted site warning.
- Click on the Run anyway option to display the stale SAML request message.
- Enter the login url again and the IDP login page displays
Chrome browser: - You may see "Connection is not private" messages -skip these warnings and the login page displays
Internet Explorer - You may see "site is not secure" or "Content was blocked because it was not signed by a valid security certificate" - skip these warnings to see the login page.
Access Denied Authentication Required error
This error typically occurs if the login is invalid, but may also occur if the max concurrent user limit has been reached. The max concurrent user limit can be configured by the server admin for in-house installations.